New reports show a fast rise in ransomware attacks across the US. Last Friday, 23 Texas towns were hit in a coordinated attack by what is believed to be a single operator as yet unidentified.
This followed earlier attacks in New York, Louisiana, Maryland, and Florida, which resulted in a significant loss, either in ransomware payments to cybercriminals or the cost of downtime, recovery, and repairs from damage caused to the computer systems and data affected.

Baltimore, in particular, struggled with weeks of computer outages and Atlanta and school districts in Louisiana most recently were painfully paralyzed by cybercriminals. Baltimore had to spend millions of dollars cleaning up after the attacks. In Florida, Riviera Beach paid $600,000 and Lake City almost $500,000 to get their data unlocked. According to reports, Lake City was covered by insurance.
Rob Gurzeev, CyCognito CEO and Co-Founder said, “Bad actors target those who are most vulnerable and generally well-funded, and unfortunately state and local municipalities fall squarely into this category. Attackers seek pathways into state and local agencies, and readily exploit paths of least resistance, such as dormant web applications, cloud computing platforms, and IT assets and third-party vendor partners whose practices and security gaps may provide a ready conduit.”
City governments have appealed to the US federal government for more help and resources to battle the growth in ransomware and other cybercrime but there is no federal agency directly in charge and no coordinated response.
Lone Star state battles cybercriminals
Texas Governor Greg Abbott issued a “Level 2 Escalated Response” following the Texas attacks. According to the Texas emergency management planning guide, this indicates “the scope of the emergency has expanded beyond that which can be handled by local responders. Normal state and local government operations may be impaired.”
Texas officials have not identified the 23 towns impacted while they seek help from US federal officials and cybersecurity experts to respond to the attacks.
According to a statement from the Texas Department of Information Resources (DIR), six state organizations are assisting in addition to Homeland Security, the FBI, FEMA, and other federal cybersecurity officials.
Texas officials warned organizations to be alert for phishing emails, suspicious links or attachments. In addition, they recommended extra diligence in verifying identities and a higher level of password security practices.
Ransomware attacks a big challenge
Speaking on CNBC, technology reporter Kate Fazzini said Baltimore and Atlanta did not pay ransomware but spent millions to clean up and restore computer operations. The smaller towns would likely have done a cost-benefit analysis and decided it was better to pay the cybercriminals to get their operations restored quickly. “It raises some thorny questions,” she said.

Some towns such as Lake City and businesses have also benefited from having insurance to cover cyber attacks. This all points to the need for smaller organizations and business to be even more vigilant and better protected against cybercrime.
Fazzini said it’s hard for most cities to respond to cybercrime. “It’s very difficult. There’s not a real infrastructure in place right now where we have one federal agency that can come in and help or respond.”
“As far as getting your networks unfrozen and dealing with the cleanup of the equipment afterward, if you decide not to pay the ransom, you have to scrap a lot of equipment,” she added. Fazzini said ransomware may simply now be the cost of doing business in today’s digital age.
Jonathan Deveaux, head of enterprise data protection at comforte AG said smishing (phishing by text message) is growing as well.” “Ransomware is still an effective way for bad actors to attempt to exploit an individual or organization to gain money. Smishing is becoming a more popular trend to attempt to fool a user to click on a link (deliver a malware-based payload) or to give up credentials.”
How to protect your organization from ransomware attacks
Being prepared for cyberattacks is a huge challenge, even for big, well-funded organizations. Most smaller entities lack substantial cybersecurity resources and expertise.
“Targeting these often unknown and unmanaged assets works well for attackers because many public sector agencies and entities fail to map their entire attacker-exposed IT ecosystem, and that creates blind spots that attackers target. Seeking solutions to map their exposed assets and ensuring their third parties are similarly rigorous are important first steps every agency can take in closing the conduits that bad actors might target,” Gurzeev advised.

“Ransomware will continue and perhaps grow with higher dollar values attached. Perpetrators do ransomware because – like phishing – it works and it can be a quick payday for them,” said Tom Garrubba, Senior Director and CISO at organization Shared Assessments.
Garrubba offered advice on how organizations can enhance protection against ransomware attacks:
- Incorporate/utilize tools and techniques to continuously identify weak spots on the network and systems (eg, outdated patches or versions that are no longer supported or can be exploited)
- Question/investigate/re-evaluate organizational information that may reside in cyberspace (eg, information on new or current market targets, initiatives, network address schematics [yes – you can find some of these out there], etc)
- Perform periodic “red team/blue team” exercises to continuously test cyber resilience
- Test your backup and recovery strategy to see if you can bring up platforms with older and unaffected but usable data
- Participate in think-tank organizations to stay abreast of risks that may affect your organization (e.g., Shared Assessments, ISAC’s, government-sponsored organizations like InfraGard).
Should you pay ransomware?
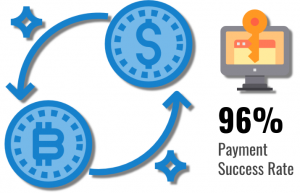
Whether organizations should pay ransomware or not is a difficult question. In most cases, it’s not disclosed or underreported at best. Research shows that in 96% of cases when ransomware is paid, victims receive decryption tools and 93% are able to recover their data. That’s not a guarantee of success however, because you’re not dealing with rational or law-abiding professionals.
Cybersecurity company Coveware reports the average ransom paid per incident during the first quarter of 2019 climbed to $12,762, compared to $6,733 in the final quarter of 2018. The average downtime has increased to 7.3 days from 6.2 days in 2018, resulting in an average cost of $64,645.
Depending on the type of attack, the cost of an incident can be much higher as Coveware’s research shows the average payment in Ryuk ransomware attacks is $286,557.

“Federal authorities continue to frown on payment to such perpetrators; however, reality can be much different when critical government services are affecting thousands of people. People want/demand their services (they expect that from their taxes or from payments made). If there’s a timeframe that needs to be met and they are unable to bring the network/systems up to a stable and usable state, they may strongly have to consider payment and then use this as a rather expensive “lesson learned” on how to better secure their systems,” Garrubba adds.
The reality is, ransomware is here to stay and is an ongoing and growing challenge. Organizations need to be proactive and plan for the possibility of cyberattacks.
Visuals courtesy Coveware, Payments NEXT

