Coveware’s Q1 Ransomware Marketplace report shows an alarming increase in ransomware incidents and the impact and costs to business in the first quarter of the year to clients of the security company.
The average ransom increased by 89% to $12,762 compared to $6,733 in Q4 of 2018. This was due to the incidence of more expensive types of ransomware such as Ryuk, Bitpaymer, and Iencrypt, which targeted larger enterprises.
How much time is lost to ransomware?

Even more concerning that the rising cost of ransomware attacks is the impact of lost time on online businesses. Coveware reports ransomware incidents cost companies an average of 7.3 days in downtime up from 6.2 days in Q4 2018.
Difficult ransomware such as Ryuk proved challenging to decrypt, resulting in substantial time lost:
“The majority of the Hermes variants are also time-consuming to decrypt with relatively high data loss rates (10-20%) compared to other types of ransomware. Downtime increased by 47% over Q4. The increase in downtime was due to the frequency of attacks where backup systems were wiped or encrypted as part of the attack, an indicator of the increasingly bespoke nature of the attacks,“ the report said.
What’s the cost of lost time?

Coveware said the average cost of lost time due to ransomware attacks was $65,645. 98% of ransoms were paid in bitcoin in advance while 2% were paid in privacy coins like Dash or Monero, usually after the incident.
These downtime costs were even bigger for companies without cyber insurance or business interruption insurance. Imagine the impact on your e-commerce business of no online sales for a week and the even bigger loss of critical data?
Cost by ransomware type
The Ryuk ransomware cost its large company targets a painful average of $286,556.70.
The Dharma ransomware cost smaller business and individuals an average of $9742.40, while GandCrab averaged $7994.50.
How much data is lost?
After a company pays the ransom attackers, recovery of data is a positive but rare outcome. Many hackers do not deliver the promised decryption tool or commonly, the decryption tool further damages files or servers resulting in little or no data recovery.
96% of companies that paid a ransom received a working decryption tool up 3% from Q4 2019 while 93% of data was recovered and 7% was lost.
Most common types of ransomware
According to the report, the most common types of ransomware were Dharma/Crysis (27.8%), GandCrab (20%), Ryuk (18.3%), Rapid (5.2%), Phobos (5.2%), Retail Diskcryptor (2.6%), and GlobeImposter 2.0 (2.6%).
The serious Ryuk ransomware showed substantial growth as hackers targeted larger organizations with “egregious” demands. Dharma was operated by less technically advanced groups, resulting in lower cost and poor recovery rates.
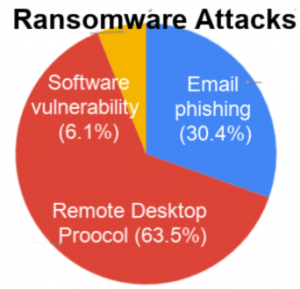
The most common attacks used were remote desktop protocols or RDP (63.5%), email phishing (30.4%), and software vulnerability (6.1%). While RDP attacks dominated, email phishing saw renewed frequency.
Which businesses are biggest targets?
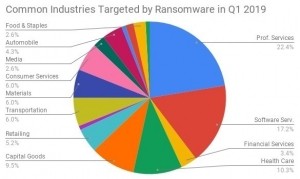
While many types of businesses were ransomware targets, the largest industries targeted included professional services firms such as lawyers and CPAs (22.4%), software services (17.2%), and smaller healthcare services firms who tend to under-invest in IT security (10.3%).
Other popular targets included capital goods (9.2%); consumer services, materials, and transportation (each 6.0%); retail (5.2%); auto (4.3%); and media (2.6%).
The average company targeted had 114 employees, up from 71 in Q4 2018, reflecting the growth in challenging ransomware attacks aimed at bigger companies.
Ransomware attacks are more sophisticated, and their financial impact is growing quickly. You can review more information on Coveware’s Q1 Ransomware Marketplace report here.
Data visuals courtesy of Coveware