
Minnesota State University infosecurity grad student Dan Salmon has a cybersecurity warning for seven million users of the popular P2P app Venmo. He recently downloaded your data to prove to Venmo that one year after they were warned by other security experts about the security of their developer API, user information is still accessible.
Check your P2P security settings
The data for the 7 million transactions were collected in three batches as part of a data security project: July 2018 – September 2018; October 2018; and Jan 2019 – Feb 2019. In his GitHub warning post, Salmon says, “I would highly encourage all users to switch their Venmo account to private by going to Settings > Privacy and selecting “Private” as well as Past Transactions > Change All to Private.”
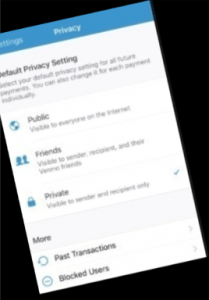
The Public by Default website has a quick six-step fix with visuals to make your past and future Venmo transactions private.
One year earlier, Mozilla Fellow and security expert Hang Do Thi Duc scraped and downloaded 207 million transactions, criticizing Venmo because payments between users are public by default.
Using Venmo API data, an entire user’s public transaction history is available, including who they shared money with, when, and in some cases for what reason — including illicit goods and substances TechCrunch reported.
Sam Bakken, Senior Product Marketing Manager, OneSpan says:
“This isn’t exactly a security vulnerability — Venmo purposely designed this functionality into their app in an effort to increase user engagement. Last summer a spokesperson said some users enjoy opening up the app to see what friends, families or strangers are purchasing via Venmo. Users do have the ability to decide whether their transactions are shared publicly or with friends or not at all. I’d argue Venmo should default to keeping users’ transactions private, and if this incident doesn’t convince Venmo to change their policy – I hope at least more people will become aware of this and consider changing their settings.”
Protect your P2P payments
P2P payment platforms like Apple Pay, Zelle, Venmo, and Cash App, provide a fast and easy way to settle restaurant bills with friends or send money to family. With their growing popularity, consumer watchdogs are also seeing an increase in P2P-related scams and fraud.

Fraud.org offers several tips to help consumers protect their P2P payments:
- Don’t use P2P services to purchase products. If an online retailer requires payment via a P2P payment service, it is probably a scam.
- Only pay with P2P services to people you know. P2P payments are meant to be used between friends and family, or with people you know well and trust, like your hairdresser or a babysitter.
- Double- and triple-check the address, username, or phone number of the person you are trying to send money to. Once the money is sent, it can be very difficult or even impossible to get the money back.
- Opt-in for stronger security. Almost every popular P2P platform offers the ability to create a personal identification number (PIN) and private settings.
Save your business from “scraping”

Ameya Talwalkar, Co-founder and CPO, Cequence Security says data scraping is a growing problem in every business, including financial institutions. “Scraping can also negatively impact companies in several ways, including lost sales and weakening of competitive advantage to competitors who are using stolen content and weakened brand awareness and loss of customer confidence when the popular products and services are more readily available at a lower price (or for free) elsewhere.”
Add to that the potential for cybercriminal theft of confidential financial and transaction information and you’ve got a recipe for business and reputation disaster. Cequence and other security companies have solutions for the data scraping problem and companies would be wise to investigate.

Meanwhile, on his Twitter account, Dan Salmon says he’s now looking for a US job opportunity in information security. He sounds exactly like the kind of smart new graduate student Venmo or any other payments company could use.

